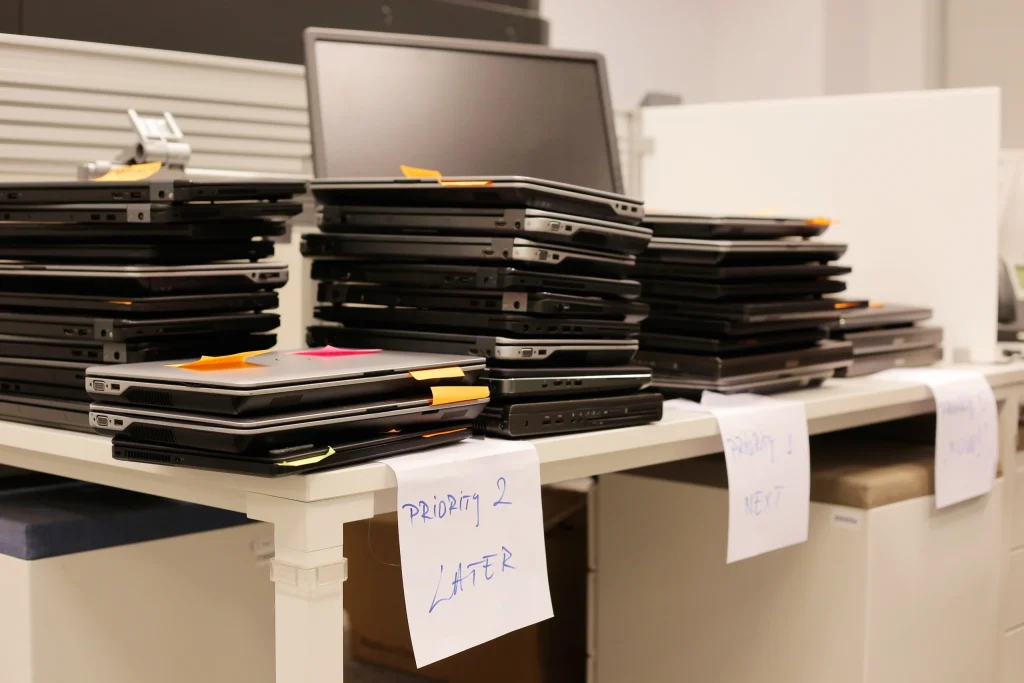
Free data destruction matters in healthcare because old devices can still carry real privacy and cybersecurity risk. If a retired laptop, hard drive, tablet, or phone once stored or accessed patient information, employee records, saved logins, or internal files, it still deserves careful handling. That is why healthcare offices looking into HIPAA-compliant computer disposal are…
Send Us a Message
[email protected]